The Internet has become an integral part of our lives, more like an extension of our physical being. Technology has become a habit. We have started depending on the web for making decisions irrespective of the matter in question, its urgency and finally, its impact. That is how sincere our faith is in technology and the internet today. From petty questions like which movie to watch over the weekend to a serious one like which doctor to consult for asthma, we rely on the web. From buying a pizza to buying a car and from booking a cab to calling an ambulance, everything is done over the internet and here comes the role of Internet of Things.
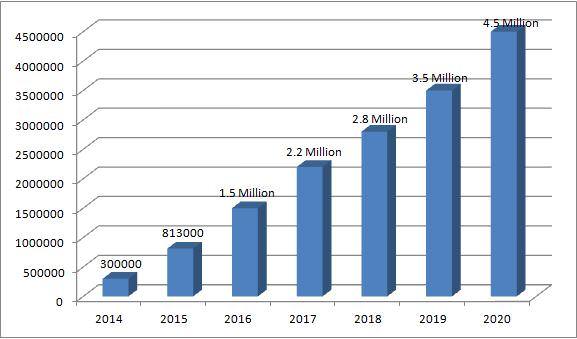
Internet of Things might have been a concept some years back but today it has become a reality. We have smart machines which are able to act according to our behaviours. The magnitude of this might be very small at the household level as of today but this is going to be huge in the future. The day is not far when most of us will be living in smart homes – a house that will inform us about a faulty wire and simultaneously, send a text to our electrician to come and fix it. Well, that is the dream most of the IoT developers are working towards. IoT is intended to create a mesh of interconnected machines and devices, talking to each other. When something this big is being executed; then, the professionals working in the field become the most significant part of the process. They say that the magnitude of IoT cannot be measured by the number of sensors but by the number of developers working on it. This statement can be understood better by observing the following graph.
Here is a projection of a number of IoT Developers from 2014 – 2020:
What happens when so many professionals are doing so much in a particular field of work? There are always speculations, doubts and questions about the viability and sustainability. The case of the Internet of Things (IoT) is no different.
One of the major issues that concern IoT professionals is its security. Security is the most critical parameter of the IoT ecosystem. With the widespread use of Wi-Fi technology and millions of devices being connected to the internet globally, the concern becomes even bigger. At the beginning of the 21st century, if someone told you that a hacker can steal your bank information from your phone, you would have laughed him off. But today, if someone states that your Facebook account can be hacked into by using your smart TV, you will pull out the wire of that television set within seconds. IoT is bound to make our lives efficient and show us a world that we can only imagine of but at the same time, it has its threats. If overlooked, IoT security can give way to a large number of cyber crimes. This is the reason why there is a lot of work being done in this area. Developers strive to make the internet platform more and more secure.
The image below shows some statistics on the Internet of Things (IoT) security vulnerabilities:
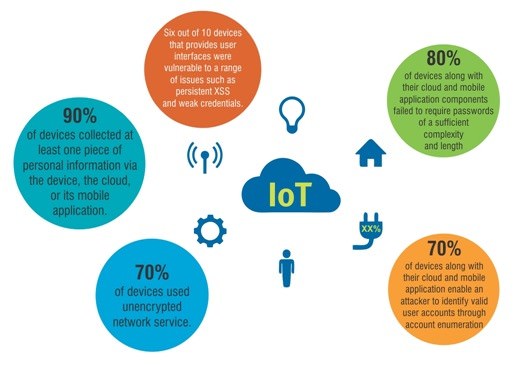
Let us observe some of the vulnerabilities in the Internet of Things (IoT) and what is being done to tackle them. Lately, the vulnerabilities found in the IoT devices have become more critical and need to be tackled quickly. At the beginning of this month, a team of researchers found critical vulnerabilities in the Internet of Things (IoT) baby monitors, which might enable the hackers to carry out some nasty stuff like monitoring live feeds, changing camera settings or even allowing other users to view or control the monitor. Scary? Consider this, the hackers can also access the internet-connected cars and manipulate the locking systems, entertainment units or even put a moving car to a halt. The effects of such hacks can be catastrophic and need to be checked well in time. Today, when we are more driven towards technology, internet-enabled wearables have become a routine commodity. These wearables are also exposed to the vulnerabilities of IoT security and at the same time, make us vulnerable to fall prey in the hands of malicious hackers. Hackers can get hold of information we type or gather our health data by getting inside these wearables. The most frightening of the IoT hacks are medical devices which can have detrimental and in worst cases, fatal effects on a person’s health.
Considering these threats, the world of the Internet of Things (IoT) has become more vigil and adamant about adopting the best security methods. Already, there are security firms who have joined hands with manufacturers to address these issues before the IoT security issues spin out of control. Digital security companies like Gemalto plan to help secure IoT devices by putting its mobile payments experience to use. Gemalto offers Secure Element Technology to automotive and utility industry. Secure Elements are tamper-resistant components which can be embedded on devices thus enabling advanced digital security and life-cycle management. This is done by encryption of and access-control limitation of sensitive data. Microsoft is also contributing to making IoT devices more secure. The company promises to add Bit Locker encryption and Secure Boot Technology to Windows 10 IoT, Microsoft’s OS for IoT devices and platforms like Raspberry Pi.
Besides these, there are a number of companies which are working towards setting up platforms which will enable large networks of IoT devices to a mutual identification and authentication. This would result in higher security and minimize the risk of data breaches. Also, there’s a lot of research being done to enhance IoT security through device and smartphone linking. Experts are of the opinion that smartphones have the capability to overcome IoT devices’ limitations in user interfaces and complexities in networking.
At Cognixia, we provide an extremely well-structured Internet of Things (IoT) Training. Our experienced trainers educate you on the nuances of the Internet of Things and prepare you for a world of opportunities. If you are fascinated by the internet, sensors and the idea of smart cities, this is just the right course for you. For further information, you can write to us




